Category: Новости
-

Decentralized vs centralized exchanges: liquidity, security and user experience
Crypto trading in 2025 feels very different from the wild days of 2017–2020. Volumes are split between huge centralized platforms and a constantly evolving DeFi ecosystem, and for many newcomers the real puzzle is simple: decentralized vs centralized exchange which is better right now? The honest answer: it depends on what you value more—liquidity, security…
-

Monthly digital asset roundup: key news, updates and market shifts you need
Why a Monthly Digital Asset Roundup Matters More Than Ever Every 30 days, the digital asset landscape quietly mutates: protocols ship upgrades, regulators tweak rules, on-chain metrics shift, and narratives rotate between AI, DeFi, and real‑world assets. A structured monthly crypto market review is not just “nice to have” anymore; it’s risk management. Instead of…
-

Beginner’s guide to buying your first digital asset: from zero to first trade
Why digital assets still matter in 2025 If ты смотришь на рынок в 2025 году и думаешь, не поздно ли заходить, то цифры говорят об обратном. По данным CoinGecko и аналитики Messari, совокупная капитализация крипторынка выросла примерно с 1,3 трлн долларов в начале 2022 года до пика выше 3,4 трлн в конце 2024-го, несмотря на…
-
Hidden risks of crypto exchanges and how to choose a secure trading platform
Hidden risks that most people ignore A quick historical detour: from hobby forums to billion‑dollar honeypots Early crypto exchanges looked more like side projects than financial infrastructure. In the beginning, trading happened on forums and through clumsy escrow services: you sent coins to a stranger and hoped they were honest. Then came the first centralized…
-
Layer 2 explained: how scaling solutions shape the future of digital assets
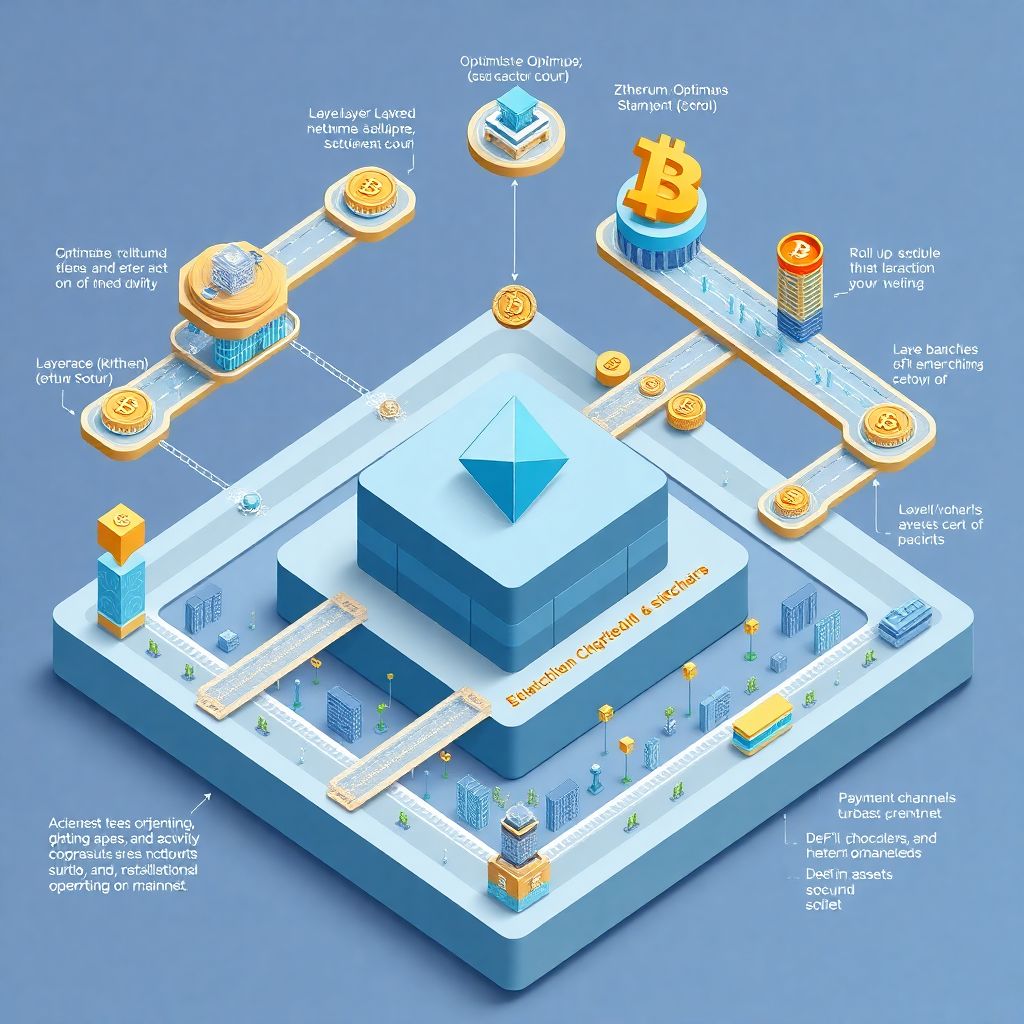
What Layer 2 Actually Is — Without the Buzzwords Layer 2 is a set of technologies built on top of existing blockchains to fix their biggest pain point: they’re too slow and too expensive when demand spikes. Instead of replacing Ethereum or Bitcoin, layer 2 scaling solutions move most activity off the main chain, then…
-

How to stay compliant with consumer protection regulations in crypto
Why crypto consumer protection suddenly matters to everyone Regulators used to treat crypto как эксперимент на обочине финансовой системы. Теперь после краха FTX, Celsius и множества мелких бирж вопрос не в том, нужны ли правила защиты потребителей, а в том, как выжить, соблюдая их. Если вы владелец биржи, DeFi‑проекта или кошелька, то «разберусь потом» уже…
-
How to secure your crypto on multi-party computation devices and prevent asset loss
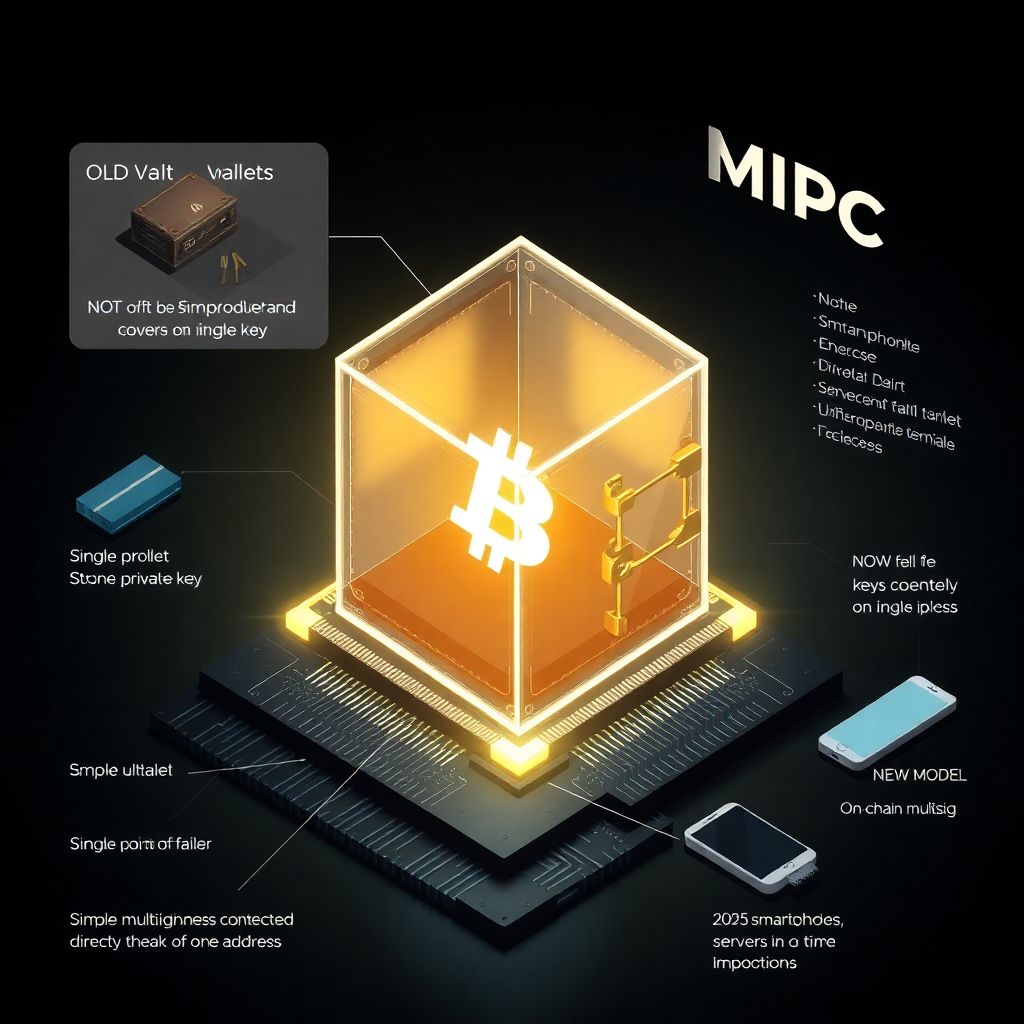
How to secure your crypto on multi-party computation devices Why MPC suddenly matters for your crypto security If вы держите заметный объём крипты, то вопрос безопасности уже нельзя решать на уровне «надеюсь, что никто не украдёт мой сид». Классическая модель с одним приватным ключом постепенно уступает место многосоставным схемам, где доступ к средствам распределён между…
-
Beginner guide to evaluating airdrop eligibility criteria and managing risk
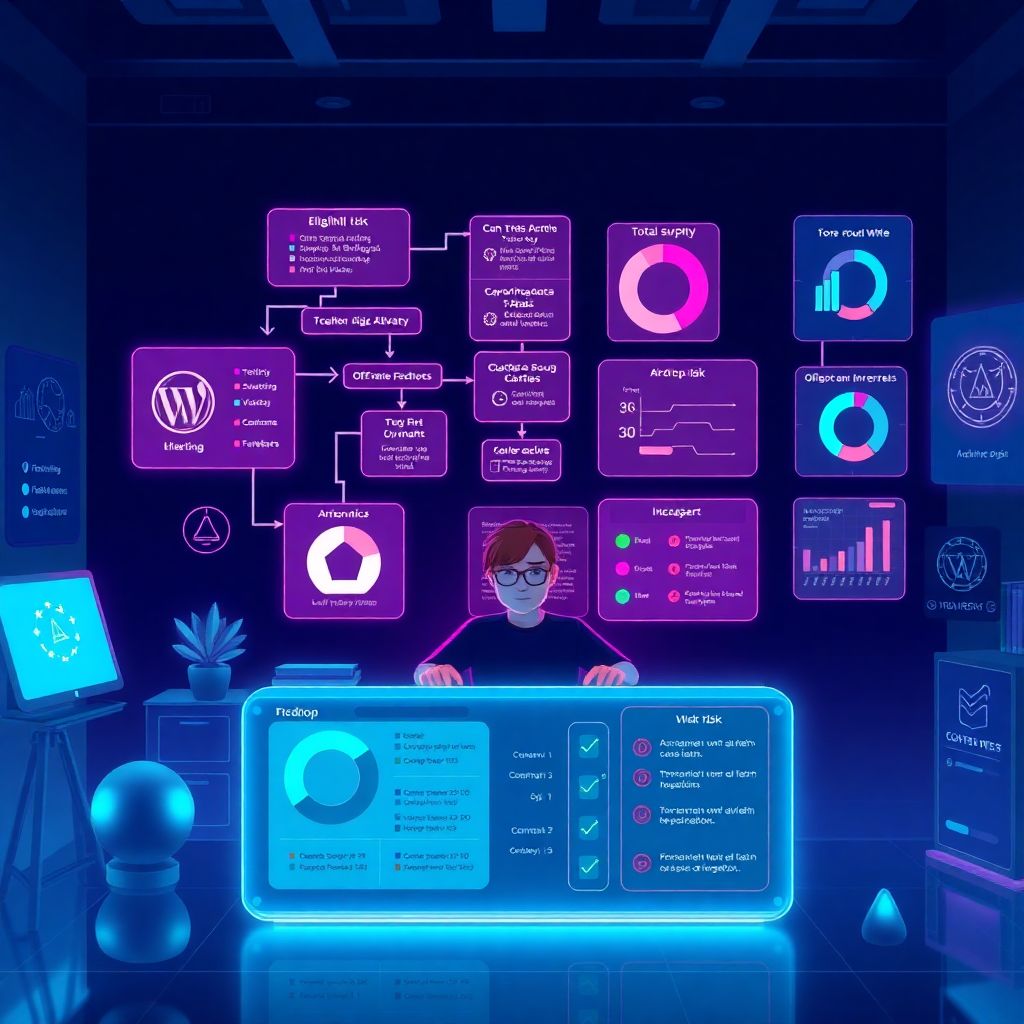
Why airdrop evaluation matters in 2025 In 2025 the airdrop world is nothing like the wild west of 2017–2021. Back then, people farmed anything with a token logo and often got rewarded just for connecting a wallet. Today, competition is higher, sybil filters are smarter, and scams are more polished. A solid crypto airdrop guide…
-

Beginner guide to mobile crypto security: choosing the best protection practices
Why mobile crypto security in 2025 is a different game Five years ago, “don’t share your seed phrase” было почти единственным советом. В 2025 мобильные кошельки превратились в полноценные финтех‑суперприложения: DeFi, NFT, P2P‑переводы, подписки на смарт‑контракты. По данным Chainalysis и разных аналитиков, в 2024 более 55–60% розничных криптотранзакций проходило через смартфоны, а число пользователей мобильных…
-

Secure cloud-based crypto storage: a practical guide to building it
Why Cloud-Based Crypto Storage Is Worth Your Time If you’re serious about crypto, sooner or later вы упрётесь в вопрос: где хранить активы так, чтобы и удобно, и безопасно. Локальные кошельки и «железки» хороши до тех пор, пока вам не нужно управлять несколькими аккаунтами, работать из разных стран или делегировать доступ команде. Вот тут и…
