Why financial privacy in crypto still matters (even if you’re “not hiding anything”)
If you trade crypto long enough, you eventually realize one uncomfortable truth: blockchains remember everything. Every deposit, every swap, every “just testing with $5” lives forever in a public ledger that anyone with a block explorer and five spare minutes can analyze. Add to that centralized exchanges that must comply with KYC rules, blockchain analytics companies tracking flows, and increasingly curious tax authorities, and “I’m anonymous because it’s crypto” stops sounding convincing. This text is meant as a down‑to‑earth crypto privacy guide for beginners: not to help anyone break the law, but to stop your entire financial life from becoming an open‑source data set for strangers, competitors, or even future employers.
Think about it this way: you probably don’t post your full bank statements on social media, even if all your money is legal and taxed. The same logic applies to on‑chain data. Once your name is connected to a specific wallet address, that address effectively becomes a transparent portfolio dashboard for anyone who cares to look. In practice, that can mean targeted scams, phishing tied to your net worth, and even physical risks in certain countries. Financial privacy is about reducing unnecessary exposure while staying compliant where you live, and doing it smartly from the start is much easier than trying to “erase” traces later, which is almost impossible on public blockchains.
Step zero: define what you actually want to protect
Before jumping into tools and fancy tricks, you need a simple threat model. Most beginners try everything at once, mixing VPNs, ten wallets, and three mixers, but still leak their data because they reuse an email or login from home Wi‑Fi. Spend five minutes and write down, literally on paper, what you want to hide and from whom. Are you mostly worried about random strangers linking your name to your holdings, or do you want to reduce data for centralized exchanges, or you just don’t want family and colleagues to be able to guess what you hold by watching your ENS or Twitter wallet? The answer changes your tactics: if the risk is street‑level crime in a high‑risk country, then you focus on hiding balances; if it’s just avoiding spam and targeted promotions, separating identities may be enough.
A simple framework is to split your “adversaries” into layers: 1) low‑effort snoopers (people who google your name); 2) determined on‑chain analysts using free tools; 3) professional analytics platforms; 4) regulators and courts. As a retail trader, you realistically aim to mitigate the first two, reduce the signal for the third, and stay entirely compliant for the fourth. This way you don’t chase unrealistic anonymity, but you do stop broadcasting every move to the entire internet. Once that’s clear, you can design a system that gives you 80% of the benefit with 20% of the effort.
Identity compartments: separate lives, separate wallets
Most privacy leaks in crypto happen not because of some advanced hack, but because people mix everything into one identity. Same email for Binance and your Telegram account, same wallet for DeFi, airdrop hunting, and long‑term holdings, same nickname for Discord, GitHub, and Twitter. If someone links one of these elements to your real name, all the rest falls like dominoes. An easy and very effective early move is to compartmentalize: personal life, trading, long‑term investing, public persona – each gets its own set of accounts and wallets, with minimal overlap between them in on‑chain transactions and off‑chain identifiers like emails and usernames.
In practice, this means at least: one “public” wallet you don’t mind attaching to your real name (for NFT mints, social features, on‑chain identity), and one or more “private” wallets where you actually hold size. You access them in different ways, with different passwords and, ideally, from different network profiles. The goal is not to be a ghost, but to ensure that if your public wallet appears in a blog post or a screenshot, nobody automatically gets your real net worth or full trading history. Many seasoned traders treat identity in layers, just like traditional businesses use different legal entities: not to be shady, but to isolate risk and information leaks.
Technical details: building basic identity layers
For beginners, a minimal setup can look like this. First, pick two hardware wallets from reputable brands if your budget allows; if not, use at least two well‑maintained software wallets with separate seed phrases. Label Wallet A as “public / experimental”, Wallet B as “private / cold”. Never connect Wallet B to random dApps; use it mostly for storage and occasional moves to and from an intermediate “hot” wallet. Create separate emails: one under your real name for KYC exchanges and tax‑relevant things, and one pseudonymous email (with strong, unique password and 2FA) for experimental platforms and accounts that don’t require legal documentation. Use a password manager to keep everything separate and avoid accidentally reusing logins across these compartments. Over time, you can add more layers, but even this simple split already stops a lot of trivial linkages.
Network privacy: VPNs, Tor, and avoiding obvious fingerprints
Your IP address and device fingerprint are the bridges between your real‑world identity and your on‑chain actions. Exchanges log them, some DeFi frontends log them, and analytics companies can sometimes correlate IP data with other leaks like cookies or social media. Using a good VPN is low‑hanging fruit. Not a free one, but a reputable paid provider with a clear privacy policy and no history of selling data; expect to pay somewhere between $3–10 per month. This doesn’t make you invisible, but it makes bulk collection and correlation harder, since your home IP is not directly attached to every on‑chain action and login.
Tor is a stronger but clunkier option. It’s a good idea when you’re accessing sensitive dashboards or checking balances on your “quiet” wallets. However, many centralized platforms either block Tor exits or heavily flag them, so don’t be surprised if your account gets extra verification requests. A nuanced approach works best: VPN as your daily driver, Tor for rare high‑privacy actions that don’t require KYC logins. Also remember basics: don’t log in to your personal Gmail in the same browser session and then immediately connect a privacy‑sensitive wallet to a DeFi dApp; cross‑site tracking is real, and browsers happily help tie things together if you let them.
Technical details: browser and device hygiene
Use separate browser profiles for different identities: for example, Chrome profile “Real Name” and Firefox profile “Trader Pseudonym.” Disable third‑party cookies where possible, and consider privacy‑focused browsers like Brave for your trading profile. Install a reputable ad‑blocker and script‑blocker, but be aware that extreme blocking can also make you stand out (“too unique” fingerprints can themselves be identifiable). On mobile, avoid mixing banking apps and high‑risk DeFi experiments on the same rooted device. Keep OS and browser updated to patch known vulnerabilities, and avoid installing random extensions; one malicious extension can log keystrokes, steal wallet phrases, or read content before it’s encrypted by HTTPS.
Choosing where you trade: balancing KYC, safety, and privacy
Fully anonymous, high‑volume trading on mainstream platforms isn’t realistic anymore. Most major exchanges enforce KYC for meaningful limits, and trying to circumvent that usually violates their terms and can get your funds frozen. Instead of chasing the impossible, you aim for a smart mix: use reputable KYC exchanges when you must touch the banking system, and use decentralized or no‑KYC venues for on‑chain‑to‑on‑chain moves with a reasonable risk profile. When you research secure and private crypto exchanges, look beyond marketing buzzwords: check their jurisdiction, history of hacks, and how they handle user data, not just their coin list and fees.
Some people assume DEXes automatically guarantee anonymity. They don’t. While you don’t submit an ID, every swap is public on‑chain. If your funding came from a KYC exchange directly into that wallet, your DEX trades can be traced back to you via on‑chain heuristics. A more privacy‑aware flow spreads your footprint: deposit from your bank to a KYC exchange, withdraw to an intermediate wallet, potentially use a privacy tool where legal, and only then interact with DeFi. Also note that regulators have started looking at large non‑KYC platforms; if a venue has a history of ignoring sanctions or AML rules, you might get short‑term anonymity but long‑term regulatory attention, which is not a good trade‑off.
Privacy coins and when they actually help
At some point you will bump into lists of the best privacy coins for secure crypto trading and wonder if you should move everything there. Coins like Monero (XMR), Zcash (especially shielded Z‑addresses), and some newer projects offer strong on‑chain privacy: hiding amounts, senders, and receivers, or at least obfuscating them heavily. For example, Monero uses ring signatures and confidential transactions by default, and typical chain‑analysis techniques that work on Bitcoin or Ethereum simply don’t apply in the same way. From the perspective of reducing your public footprint, this can be extremely effective.
However, privacy coins exist under a political microscope. Some centralized exchanges have delisted them under pressure from regulators, or restrict their availability in specific countries. Liquidity can also be thinner compared to blue‑chip assets, leading to higher slippage on big orders. A pragmatic strategy is to treat privacy coins as a temporary “dark room”: move funds in for obfuscation or private holdings, then bridge back out when needed, instead of trying to build your entire trading stack on them. Always check the legal status in your jurisdiction; in some places, holding them is fine, in others, regulators explicitly dislike them, which can complicate future on‑ramps and off‑ramps.
Technical details: example privacy coin workflow
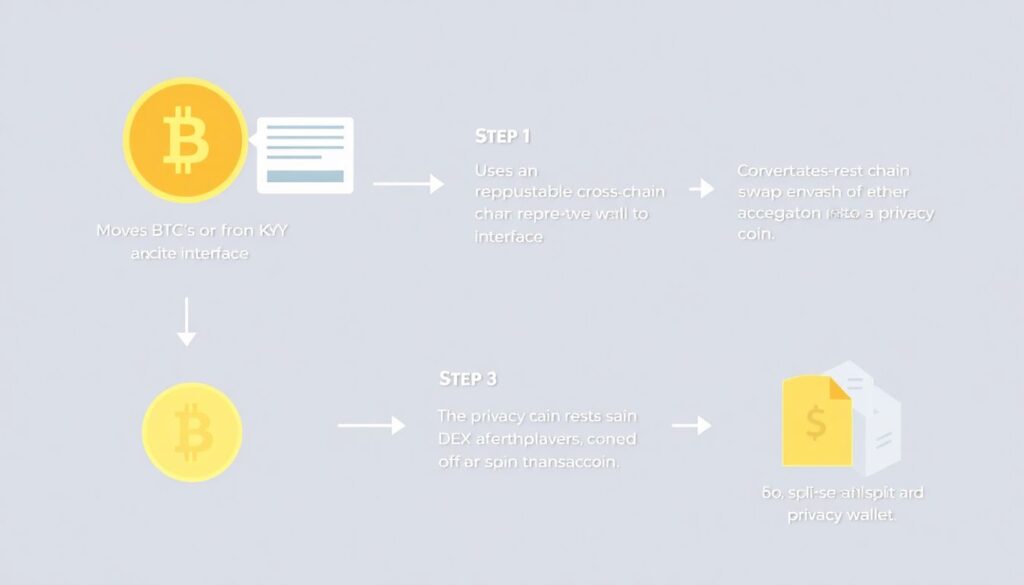
A simplified, legality‑aware flow could be: 1) move BTC or USDT from a KYC exchange to your own wallet; 2) use a reputable cross‑chain swap or DEX aggregator to convert part of it into a privacy coin; 3) let it “rest” in a private wallet and, if your risk model allows, split it into several transactions over time; 4) later, convert back into a more liquid asset through a non‑custodial swap service or a DEX. The key is to avoid looping the exact same amount in a short time frame, which makes your pattern trivial to match. Use amounts and timings that blend in with ordinary traffic. Even then, remember that once you interact again with KYC rails, large suspicious patterns may be questioned, so keep good records for legitimate explanations.
Bitcoin and Ethereum privacy: doing better than nothing
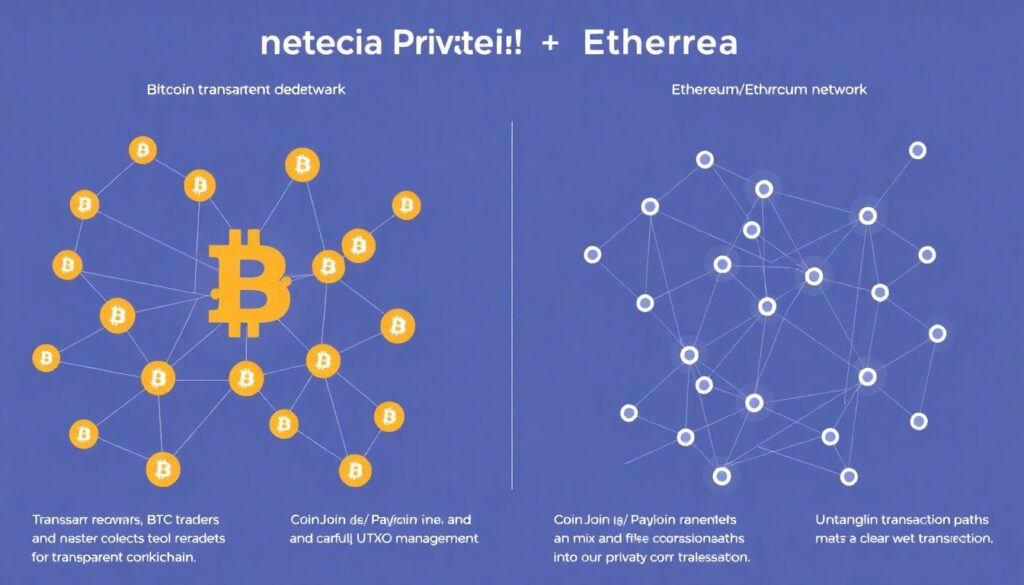
If you mostly trade BTC or ETH, you are on very transparent networks. Still, there are realistic tools that improve your situation significantly. On Bitcoin, techniques like CoinJoin, PayJoin, and simple UTXO management help untangle your transaction graph. On Ethereum and EVM chains, you don’t have UTXOs, but you can still separate addresses, avoid obvious linkages, and use privacy layers where legal, such as on‑chain mixers or L2s that reduce visible detail. None of this guarantees you’ll be untraceable to a determined investigator, but it does remove you from the category of “low‑hanging fruit” whose complete history is visible with one block‑explorer query.
For example, imagine you withdraw 0.5 BTC from an exchange directly to the same address you use for your NFT identity, DeFi degens, and personal ENS name. From that point on, your friends, Twitter followers, and any script kiddie can see your approximate holdings. If instead you withdraw to a fresh address, run a CoinJoin with dozens of peers, and then send smaller randomized outputs to a separate long‑term wallet, you’ve made that linkage much harder. The same idea on Ethereum would mean funding different addresses for experimentation and for storage, and avoiding sending everything back and forth between them in clear one‑to‑one amounts.
Technical details: specific privacy tools and numbers
On Bitcoin, tools like Wasabi Wallet and Samourai‑style CoinJoin implementations (where available in your jurisdiction) group your inputs with those of many other users. A single CoinJoin round may include dozens of participants and dozens of outputs; the goal is to create ambiguity so analytics can’t easily tell which output belongs to which input. Some users run multiple rounds to increase entropy, at the cost of additional fees and time. On Ethereum, privacy‑preserving schemes historically included protocols like Tornado Cash, which has since faced heavy sanctions and regulatory action; using such tools can be illegal in some jurisdictions. A more conservative approach is simple address hygiene, L2 usage with batched transactions, and minimizing public linking of addresses through ENS and on‑chain identity services. Always check current regulations; this area changes fast.
Non‑obvious leaks: NFTs, airdrops, and social bragging
Many beginners carefully set up VPNs and new wallets, then blow their privacy by minting an NFT from their “secret” wallet and proudly posting it on social media. Or they connect the same wallet to ten airdrop‑hunter platforms that require Twitter or Discord verification, effectively doxing their address to every project admin and sometimes exposed databases. These side activities are surprisingly powerful for deanonymization: a simple public ENS that points to your main address can destroy a year of careful operational security in one click, especially if you used that ENS in a context tied to your real name.
The non‑standard but practical solution is to treat NFTs and airdrops like you would treat email newsletters: they belong to a noisy, disposable identity, not your serious financial one. Have a dedicated “farm” wallet that does mints, quests, and social tasks, with only limited balances you’re willing to risk. When you decide to cash out or transfer value from that noisy wallet to your quiet holdings, consider using intermediate hops or, where legal, privacy tools, and avoid mirroring exact balances. Between 2020 and 2023, several public datasets of airdrop claimants and NFT buyers were leaked or scraped, making it trivial to link user handles to on‑chain addresses; assume that anything you connect to a public profile will be harvested sooner or later.
Trading anonymously vs. trading discreetly
A lot of people search for “how to trade cryptocurrency anonymously” expecting a magic checklist that makes them invisible. The honest version is less glamorous: true anonymity against state‑level observers isn’t realistically achievable for the average retail trader who touches banks, big exchanges, or major stablecoins. The better and more sustainable goal is discretion: ensuring that your colleagues, extended family, random scammers, and low‑effort attackers can’t trivially connect your real identity to exact holdings and past trades. That’s achievable with consistent but not extreme habits.
Discreet trading means accepting KYC where you must, but minimizing the on‑chain footprint that leaks from your KYC entities into your private life. For instance, you might use a KYC exchange solely as the bridge between fiat and crypto, withdrawing to new addresses each time and never reusing deposit addresses from public wallets. You keep detailed private records for taxes and compliance, but you don’t hand over a perfectly labeled public blockchain history to every curious onlooker for free. By aiming for discretion instead of absolute anonymity, you also avoid the trap of over‑engineering your setup so much that you start making operational mistakes or triggering red flags with chaotic transaction patterns.
Protecting your real‑world identity: data discipline
On‑chain privacy is only half the story. Many traders leak more through sloppy account setups than through transactions themselves. Using your full name in exchange support tickets, reusing the same username across Reddit, Telegram, and trading forums, or submitting ID documents without checking the domain carefully can all undermine whatever you do with wallets and mixers. If you really care about how to protect your identity in crypto trading, you must treat personal data as a scarce resource, not something you hand out casually in every signup form.
Concretely, avoid posting screenshots that reveal order sizes, account balances, or parts of email addresses and IDs; cropped images can still contain metadata, and people routinely underestimate how much can be reconstructed. When supporting documents are required, upload them only through official channels and double‑check URLs; phishing domains mimicking big exchanges have stolen countless IDs and selfies. Where possible, use minimal disclosure: if a platform allows partial redaction of non‑essential data in documents (legally and within their rules), take advantage of it. And never send your seed phrase or private key “to support” – legitimate services will never ask for it, yet people still fall for this daily.
Technical details: passwords, 2FA, and SIM‑swap risk
Use a password manager and aim for unique, randomly generated passwords of at least 16 characters for each account. For 2FA, prefer authenticator apps (TOTP) or hardware security keys over SMS, which is vulnerable to SIM‑swap attacks. A common real‑world case: someone has good on‑chain privacy but secures their main exchange with a weak password and SMS 2FA; an attacker convinces the telecom provider to port the phone number, resets the password, drains the account, and now also can see some of the victim’s transaction history. Consider dedicating a separate phone number or even a separate device to handle 2FA for high‑value services, and never post that number publicly or use it for unrelated social media profiles.
Thinking in flows, not isolated actions
The biggest mindset shift in privacy is to stop thinking in terms of isolated tricks and start thinking in transaction flows. One clean address is useless if it regularly sends funds to your public address in neat, round numbers. One VPN doesn’t help much if you repeatedly log in from your home IP because it’s “more convenient this time.” Instead, sketch your typical flows: fiat → exchange → wallets → DEXes → storage, and look for links that would let an outside observer follow the money with little effort. Your job is to break or blur those links without breaking the law or your own ability to account for funds.
Non‑standard solutions often come from slightly re‑architecting these flows. For example, a professional trader might maintain a small “buffer” wallet per strategy, so each trading system leaves a distinct but limited footprint, rather than one mega‑wallet that shows every experiment. Another practical trick is using time as a variable: instead of instantly moving the exact amount you just received, wait, split, and recombine based on your privacy budget. Over a year, this smooths your graph and makes pattern recognition harder, while still letting you produce clean internal records for accounting and regulation.
Simple action plan for beginners
To make this less abstract, here is a compact, realistic plan you can implement over a weekend. It doesn’t make you a ghost, but it boosts your privacy dramatically compared to doing nothing and aligns well with what a crypto privacy guide for beginners should recommend.
1. Define your threat model
Decide who you’re protecting yourself from (random snoopers, scammers, not your tax agency) and what you want to keep private (balances, trade history, wallet connections). Write it down to avoid chasing unrealistic goals.
2. Create separate identities and wallets
Set up at least two email addresses and two wallet sets (public / experimental vs private / storage). Never connect your storage wallet to random dApps, and don’t reuse emails between personal life and trading persona.
3. Fix your network and browser setup
Subscribe to a reputable VPN, create separate browser profiles for trading, and install minimal, well‑audited privacy extensions. Avoid logging into personal accounts in the same session you use for sensitive wallet actions.
4. Choose trading venues consciously
Use reputable KYC exchanges only as fiat on‑ and off‑ramps, and prefer non‑custodial DEXes for on‑chain swaps. When looking for the most secure and private crypto exchanges, prioritize data‑handling practices and jurisdiction, not only low fees.
5. Add privacy layers gradually
Learn basic UTXO management for Bitcoin, use separate addresses on Ethereum, and experiment cautiously with privacy coins where legal. Keep written records so you can always explain flows if needed for compliance.
6. Audit your public footprint
Search your own name, nicknames, and wallet addresses. Check past posts for screenshots, ENS registrations, or NFT mints that reveal more than you’d like. Where possible, de‑link or migrate public wallets away from serious holdings.
Final thoughts: privacy as an ongoing habit, not a one‑time setup
Financial privacy in crypto isn’t something you “finish” in an afternoon. Networks evolve, regulations change, and your own habits drift over time. The goal is not perfection; it’s to build a lifestyle where privacy‑friendly defaults are easier than risky ones. If you make it normal for yourself to separate identities, use a VPN, think in flows, and question every new connection between your real name and your wallets, you’ll stay far ahead of most retail users in terms of protection.
Above all, remember that discretion doesn’t have to turn you into a paranoid recluse. You can still enjoy the social side of crypto, show off art, contribute to DAOs, and talk about your strategies. You just don’t have to do all of that from the same address that holds your savings or reveals your full history. With a bit of planning and consistent discipline, you can trade actively, stay compliant, and keep your financial life from becoming a public reality show.

